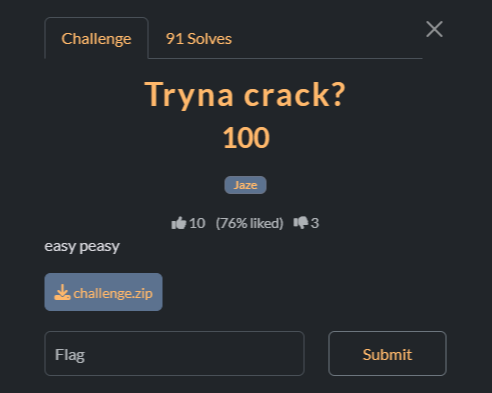
Đề bài
Giải
Bài này cho mình 1 file zip
Sau đó mình thử unzip file zip thì thấy cần passwd
$ unzip challenge.zip
Archive: challenge.zip
[challenge.zip] quackquackquack.png password:
Mình thử crack bằng john
$ zip2john challenge.zip > zip.hash
john zip.hash --wordlist=/usr/share/wordlists/rockyou.txt
ver 1.0 efh 5455 efh 7875 challenge.zip/quackquackquack.png PKZIP Encr: 2b chk, TS_chk, cmplen=19730, decmplen=19718, crc=5CE4AC7D ts=4A03 cs=4a03 type=0
Using default input encoding: UTF-8
Loaded 1 password hash (PKZIP [32/64])
Will run 8 OpenMP threads
Note: Passwords longer than 21 [worst case UTF-8] to 63 [ASCII] rejected
Press 'q' or Ctrl-C to abort, 'h' for help, almost any other key for status
0g 0:00:00:05 DONE (2025-10-31 21:50) 0g/s 2753Kp/s 2753Kc/s 2753KC/s "2parrow"..*7¡Vamos!
Session completed.
john cũng không crack được passwd cho file zip này, sau một hồi tìm kiếm thì mình thấy nó là dạng ZipCrypto
$ printf '\x89PNG\r\n\x1a\n\x00\x00\x00\x0D\x49\x48\x44\x52' > known.bin
$ /tmp/bkcrack-1.7.0-Linux/bkcrack \
-C challenge.zip -c quackquackquack.png \
-p known.bin -o 0
bkcrack 1.7.0 - 2024-05-26
[22:08:15] Z reduction using 9 bytes of known plaintext
100.0 % (9 / 9)
[22:08:16] Attack on 783459 Z values at index 6
Keys: 4672d551 bcb3adcb c76d52c5
44.5 % (348408 / 783459)
Found a solution. Stopping.
You may resume the attack with the option: --continue-attack 348408
[22:41:56] Keys
4672d551 bcb3adcb c76d52c5
$ /tmp/bkcrack-1.7.0-Linux/bkcrack \
-C challenge.zip -c quackquackquack.png \
-k 4672d551 bcb3adcb c76d52c5 -d quack.png
bkcrack 1.7.0 - 2024-05-26
[22:59:35] Writing deciphered data quack.png
Wrote deciphered data (not compressed).
Sau đó mình nhận được ảnh như sau
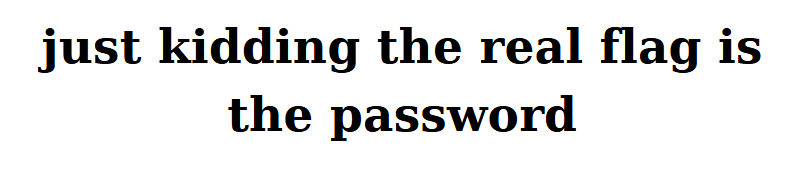
Mình thử exiftool thì thấy đoạn comment sau nhưng lại không phải flag, chắc có gì đó
$ exiftool quackquackquack.png
ExifTool Version Number : 13.25
File Name : quackquackquack.png
Directory : .
File Size : 20 kB
File Modification Date/Time : 2025:10:16 20:16:06+07:00
File Access Date/Time : 2025:10:31 23:39:37+07:00
File Inode Change Date/Time : 2025:10:31 23:39:14+07:00
File Permissions : -rwxrwxrwx
File Type : PNG
File Type Extension : png
MIME Type : image/png
Image Width : 806
Image Height : 184
Bit Depth : 8
Color Type : RGB with Alpha
Compression : Deflate/Inflate
Filter : Adaptive
Interlace : Noninterlaced
Exif Byte Order : Little-endian (Intel, II)
User Comment : password for zip file =)))) D4mn_br0_H0n3y_p07_7yp3_5h1d
SRGB Rendering : Perceptual
Gamma : 2.2
Pixels Per Unit X : 3779
Pixels Per Unit Y : 3779
Pixel Units : meters
Image Size : 806x184
Megapixels : 0.148
Ở đây mình sử dụng tool fotoforensics để kiểm tra ảnh này

Mình thấy một đoạn mã morse sau: ... .... .- ..... .---- ..---
Giải mã ra sẽ là: 215AHS
Đảo ngược lại sẽ thành SHA512, vậy ghép lại thành "just kidding the real flag is the password in sha512"

Flag
Flag: v1t{7083748baa3a42dc0a93811e4f5150e7ae1a050a0929f8c304f707c8c44fc95d86c476d11c9e56709edc30eba5f2d82396f426d93870b56b1a9573eaac8d0373}
'WriteUp > Forensics' 카테고리의 다른 글
| Hidden in plainsight - picoCTF (0) | 2025.11.04 |
|---|---|
| Riddle Registry - picoCTF (0) | 2025.11.04 |
| [Forensics] CovertS - CSCV 2025 (0) | 2025.10.20 |
| [Forensics] Quack - Dreamhack (0) | 2025.10.20 |
| [Forensics] Nimbus - POC CTF 2025 (0) | 2025.10.20 |
