Đề bài
Giải
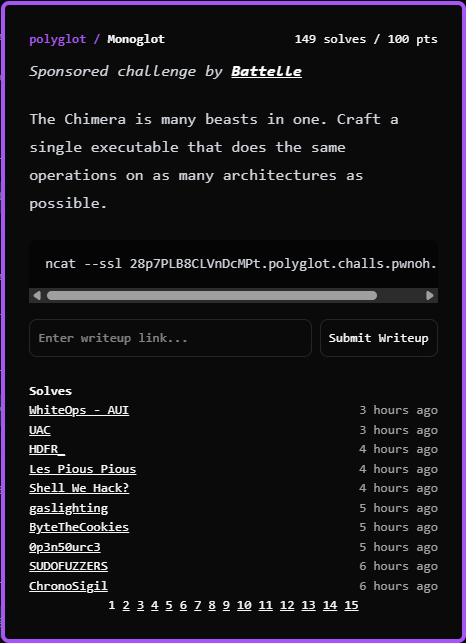
Bài này mình sẽ để vào Pwn vì nó là dạng viết shellcode sao cho nó hoạt động được trên càng nhiều kiến trúc càng tốt
┌──(kali㉿kali)-[/BuckeyeCTF 2025/polygot]
└─$ ncat --ssl 28p7PLB8CLVnDcMPt.polyglot.challs.pwnoh.io 1337
╭──────────────────────────────────────────────────────────────────────────────────╮
│ │
│ Polyglot │
│ │
╰──────────────────────────────────────────────────────────────────────────────────╯
Craft a single binary chimera that is the same bytes but runs on many architectures.
Supported architectures:
• arm_le
• arm_be
• arm_thumb_le
• aarch64_le
• mips_le
• mips_be
• x86
• x86_64
• riscv64
• powerpc32
Goal:
• Syscall number: 237
• Arg1: 38085
• Arg2: pointer to the string "Battelle"
Submit your shellcode (in hex):
>Script
#!/usr/bin/env python3
from pwn import *
import subprocess
context.log_level = "error"
SYS = 237
ARG1 = 38085
S = "Battelle"
def sc_x86():
context.clear(arch='i386', os='linux', endian='little')
asm_code = f"""
jmp str
back:
pop ecx
mov eax, {SYS}
mov ebx, {ARG1}
int 0x80
str:
call back
.ascii "{S}\\0"
"""
return asm(asm_code)
def sc_x64():
context.clear(arch='amd64', os='linux', endian='little')
asm_code = f"""
jmp str
back:
pop rsi
mov rax, {SYS}
mov rdi, {ARG1}
syscall
str:
call back
.ascii "{S}\\0"
"""
return asm(asm_code)
def sc_arm_le():
context.clear(arch='arm', os='linux', endian='little')
asm_code = f"""
adr r1, str
movw r0, #{ARG1 & 0xffff}
mov r7, #{SYS}
svc 0
str:
.ascii "{S}\\0"
"""
return asm(asm_code)
def sc_aarch64_le():
context.clear(arch='aarch64', os='linux', endian='little')
asm_code = f"""
adr x1, str
mov x0, #{ARG1}
mov x8, #{SYS}
svc 0
str:
.ascii "{S}\\0"
"""
return asm(asm_code)
def sc_mips_le():
context.clear(arch='mips', os='linux', endian='little')
asm_code = f"""
.set noreorder
bal getpc
nop
getpc:
addu $t0, $ra, $zero
addiu $a1, $t0, str - getpc
li $a0, {ARG1}
li $v0, {SYS}
syscall
str:
.ascii "{S}\\0"
"""
return asm(asm_code)
mips_le = ", ".join(hex(b) for b in sc_mips_le())
i386 = ", ".join(hex(b) for b in sc_x86())
amd64 = ", ".join(hex(b) for b in sc_x64())
arm_le = ", ".join(hex(b) for b in sc_arm_le())
a64 = ", ".join(hex(b) for b in sc_aarch64_le())
asm_template = r"""
bits 32
global _start
_start:
; MIPS-LE / x86 junk
db 0x04, 0x00, 0x04, 0x10
; x86/x64: jmp _x86 (0xeb ..)
; arm/arm64: harmless
db 0xeb, (_x86 - $ - 2), 0x32, 0x32
; arm: b _arm
; arm64: ands x1, x0, x0
db ((_arm - $ - 8) / 4), 0x00, 0x00, 0xea
; arm64: b _arm64
; arm: andeq r0, r0, r0
db ((_arm64 - $) / 4), 0x00, 0x00, 0x14
; -------- MIPS-LE --------
times (4 - (($ - _start) % 4)) nop
_mips:
db {mips_le}
; -------- x86 / x86_64 dispatch --------
_x86:
xor eax, eax
db 0x40
nop
jz _x86_64
_x86_32:
db {i386}
_x86_64:
db {amd64}
; -------- ARM-LE --------
times (4 - (($ - _start) % 4)) nop
_arm:
db {arm_le}
; -------- AARCH64-LE --------
times (4 - (($ - _start) % 4)) nop
_arm64:
db {a64}
"""
asm_src = asm_template.format(
mips_le=mips_le,
i386=i386,
amd64=amd64,
arm_le=arm_le,
a64=a64,
)
with open("chimera.asm", "w") as f:
f.write(asm_src)
subprocess.check_call(["nasm", "-fbin", "-o", "chimera.bin", "chimera.asm"])
data = open("chimera.bin", "rb").read()
print(data.hex())Flag
Monoglot flag: bctf{a_good_start_4fc9c43c0d95}
Diglot flag: bctf{now_you_are_bilingual_d9731b3bf6bf}
Triglot flag: bctf{you_are_a_true_polyglot_25afd5c411f9}
Tetraglot flag: bctf{Du_bist_ein_wahrer_Polyglott_47d86e5a3934}
Pentaglot flag: bctf{du_er_en_sand_polyglot_16b4cea477d1}
