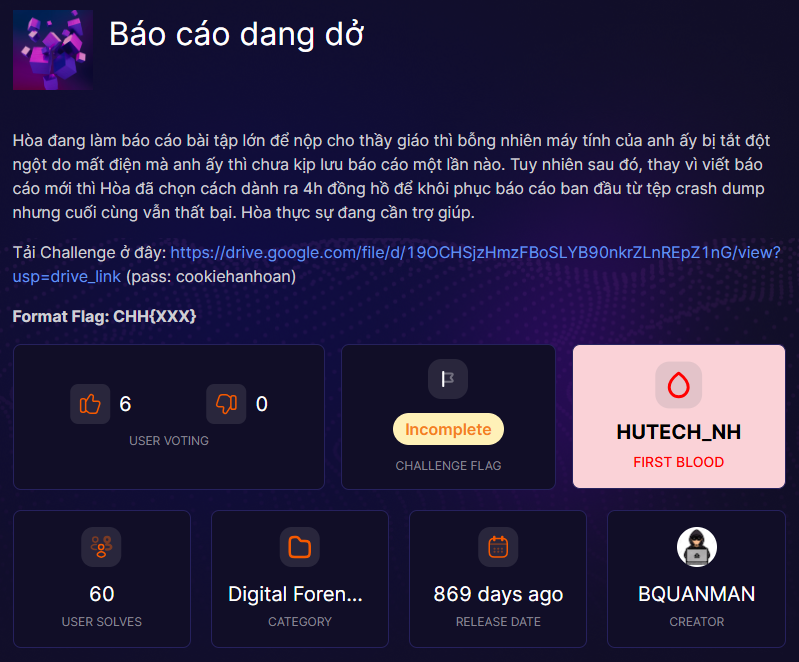
Đề bài
Giải
Bài này cho mình Memory File của Windows
$ file MEMORY.DMP
MEMORY.DMP: MS Windows 64bit crash dump, version 15.7601, 2 processors, DumpType (0x1), 524158 pagesVới Mem File thì mình sẽ tiếp tục dùng Volatility3 thôi
pslist
$ vol3 -f MEMORY.DMP windows.pslist
Volatility 3 Framework 2.26.2
/home/kali/volatility3/volatility3/framework/deprecation.py:105: FutureWarning: This plugin (PluginRequirement) has been renamed and will be removed in the first release after 2026-06-01. PluginRequirement is to be deprecated. Use VersionRequirement instead.
warnings.warn(
Progress: 100.00 PDB scanning finished
PID PPID ImageFileName Offset(V) Threads Handles SessionId Wow64 CreateTime ExitTime File output
4 0 System 0xfa80024bb840 90 512 N/A False 2023-05-31 18:18:24.000000 UTC N/A Disabled
268 4 smss.exe 0xfa8002c5e400 2 30 N/A False 2023-05-31 18:18:24.000000 UTC N/A Disabled
356 340 csrss.exe 0xfa80037e7060 9 451 0 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
440 340 wininit.exe 0xfa8003a68060 3 79 0 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
460 448 csrss.exe 0xfa8003a67060 10 231 1 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
520 448 winlogon.exe 0xfa8003ab6700 3 111 1 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
528 440 services.exe 0xfa8003ab7810 7 207 0 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
564 440 lsass.exe 0xfa8003aeab30 9 570 0 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
572 440 lsm.exe 0xfa8003aec810 10 144 0 False 2023-05-31 18:18:26.000000 UTC N/A Disabled
672 528 svchost.exe 0xfa8003b6e3c0 10 356 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
732 528 vmacthlp.exe 0xfa8003b9fb30 3 56 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
768 528 svchost.exe 0xfa8003bd3b30 9 292 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
868 528 svchost.exe 0xfa8003c18060 20 480 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
924 528 svchost.exe 0xfa8003c52b30 16 377 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
952 528 svchost.exe 0xfa8003c613a0 42 1036 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
400 528 svchost.exe 0xfa8003cb24b0 12 542 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
856 528 svchost.exe 0xfa8003ce3b30 15 364 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
1116 528 spoolsv.exe 0xfa8003d6f250 15 338 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
1148 528 svchost.exe 0xfa8003d91b30 19 316 0 False 2023-05-31 18:18:27.000000 UTC N/A Disabled
1340 924 dwm.exe 0xfa8003e38b30 5 124 1 False 2023-05-31 18:18:28.000000 UTC N/A Disabled
1372 1304 explorer.exe 0xfa8003e64960 39 1058 1 False 2023-05-31 18:18:28.000000 UTC N/A Disabled
1472 528 taskhost.exe 0xfa8003ea8410 8 145 1 False 2023-05-31 18:18:28.000000 UTC N/A Disabled
1544 528 VGAuthService. 0xfa8003f23b30 3 85 0 False 2023-05-31 18:18:28.000000 UTC N/A Disabled
1684 528 vmtoolsd.exe 0xfa8003f6f200 9 293 0 False 2023-05-31 18:18:28.000000 UTC N/A Disabled
1928 1372 vmtoolsd.exe 0xfa800407db30 6 186 1 False 2023-05-31 18:18:29.000000 UTC N/A Disabled
1288 528 svchost.exe 0xfa8004087060 5 103 0 False 2023-05-31 18:18:29.000000 UTC N/A Disabled
1316 672 WmiPrvSE.exe 0xfa8004b03060 10 211 0 False 2023-05-31 18:18:29.000000 UTC N/A Disabled
2136 528 dllhost.exe 0xfa8004b05b30 15 207 0 False 2023-05-31 18:18:29.000000 UTC N/A Disabled
2288 528 msdtc.exe 0xfa8004480b30 14 154 0 False 2023-05-31 18:18:30.000000 UTC N/A Disabled
2564 528 SearchIndexer. 0xfa80045344a0 13 616 0 False 2023-05-31 18:18:34.000000 UTC N/A Disabled
2844 672 WmiPrvSE.exe 0xfa80045b8530 10 239 0 False 2023-05-31 18:18:49.000000 UTC N/A Disabled
1736 1372 WINWORD.EXE 0xfa8003a6e060 13 443 1 False 2023-05-31 18:20:18.000000 UTC N/A Disabled
2792 528 svchost.exe 0xfa8003c86920 5 74 0 False 2023-05-31 18:20:18.000000 UTC N/A Disabled
2956 528 OSPPSVC.EXE 0xfa8003fcab30 3 129 0 False 2023-05-31 18:20:19.000000 UTC N/A Disabled
1916 528 svchost.exe 0xfa8003f83b30 12 321 0 False 2023-05-31 18:20:29.000000 UTC N/A Disabled
2484 868 audiodg.exe 0xfa8003c83b30 6 136 0 False 2023-05-31 18:26:32.000000 UTC N/A Disabled
1076 2228 taskmgr.exe 0xfa8004103b30 9 121 1 False 2023-05-31 18:27:43.000000 UTC N/A DisabledThấy có một tiến trình khá lạ là PID 1736 với process là WINWORD.exe
handles
Tiếp theo mình sẽ check các file mà WINWORD.exe đã mở
$ vol3 -f MEMORY.DMP windows.handles --pid 1736Kết quả ra khá dài nên mình chỉ để lệnh thôi
Mình phát hiện thấy có một file được mở sau
1736 WINWORD.EXE 0xfa8003d5c860 0x448 File 0x12019f \Device\HarddiskVolume2\Users\admin\AppData\Roaming\Microsoft\Templates\Normal.dotm
dumpfiles
Mình sẽ dump file này ra
$ mkdir -p dumps
vol3 -f MEMORY.DMP -o dumps windows.dumpfiles --virtaddr 0xfa80041e2070
Volatility 3 Framework 2.26.2
/home/kali/volatility3/volatility3/framework/deprecation.py:105: FutureWarning: This plugin (PluginRequirement) has been renamed and will be removed in the first release after 2026-06-01. PluginRequirement is to be deprecated. Use VersionRequirement instead.
warnings.warn(
Progress: 100.00 PDB scanning finished
Cache FileObject FileName Result
DataSectionObject 0xfa80041e2070 AutoRecovery save of Document1.asd file.0xfa80041e2070.0xfa8003d7b6d0.DataSectionObject.AutoRecovery save of Document1.asd.datChuyển nó ra ngoài và đổi tên cho ngắn
$ mv dumps/file.0xfa80041e2070.0xfa8003d7b6d0.DataSectionObject.AutoRecovery\ save\ of\ Document1.asd.dat Document1.asdPhân tích
Kiểm tra file vừa dump ra
$ file Document1.asd
Document1.asd: Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: admin, Template: Normal, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Total Editing Time: 06:00, Create Time/Date: Sun Apr 30 18:20:00 2023, Number of Pages: 3, Number of Words: 136, Number of Characters: 778, Security: 0Đây là file word bình thường, mình sẽ extract bằng binwalk ra luôn
$ binwalk -e Document1.asd
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
16762 0x417A Zip archive data, at least v2.0 to extract, compressed size: 255, uncompressed size: 540, name: [Content_Types].xml
17066 0x42AA Zip archive data, at least v2.0 to extract, compressed size: 192, uncompressed size: 310, name: _rels/.rels
17299 0x4393 Zip archive data, at least v2.0 to extract, compressed size: 131, uncompressed size: 138, name: theme/theme/themeManager.xml
17488 0x4450 Zip archive data, at least v2.0 to extract, compressed size: 1734, uncompressed size: 6795, name: theme/theme/theme1.xml
19274 0x4B4A Zip archive data, at least v2.0 to extract, compressed size: 182, uncompressed size: 283, name: theme/theme/_rels/themeManager.xml.rels
20210 0x4EF2 Zip archive data, at least v2.0 to extract, compressed size: 165, uncompressed size: 197, name: [Content_Types].xml
21752 0x54F8 Zip archive data, at least v2.0 to extract, compressed size: 252, uncompressed size: 467, name: [Content_Types].xml
22573 0x582D Zip archive data, at least v2.0 to extract, compressed size: 188, uncompressed size: 301, name: _rels/.rels
23322 0x5B1A Zip archive data, at least v2.0 to extract, compressed size: 804, uncompressed size: 3002, name: word/drawings/drawing1.xml
24182 0x5E76 Zip archive data, at least v2.0 to extract, compressed size: 198, uncompressed size: 427, name: word/drawings/_rels/drawing1.xml.rels
24447 0x5F7F Zip archive data, at least v1.0 to extract, compressed size: 443854, uncompressed size: 443854, name: word/media/image2.png
468352 0x72580 Zip archive data, at least v1.0 to extract, compressed size: 40015, uncompressed size: 40015, name: word/media/image1.png
WARNING: One or more files failed to extract: either no utility was found or it's unimplementedTrong image2 thấy có ảnh chứa flag

Flag
Flag: CHH{4ut0R3c0v3r_s4v3_my_l1f3}
'WriteUp > Forensics' 카테고리의 다른 글
| Forensics - ESCHATON CTF Quals 2026 (0) | 2026.03.01 |
|---|---|
| Forensics - VSL CTF 2026 (0) | 2026.01.26 |
| Under Control - Cookie Arena (0) | 2025.11.22 |
| Masks Off - HackTheBox (0) | 2025.11.21 |
| emo - HackTheBox (0) | 2025.11.21 |
